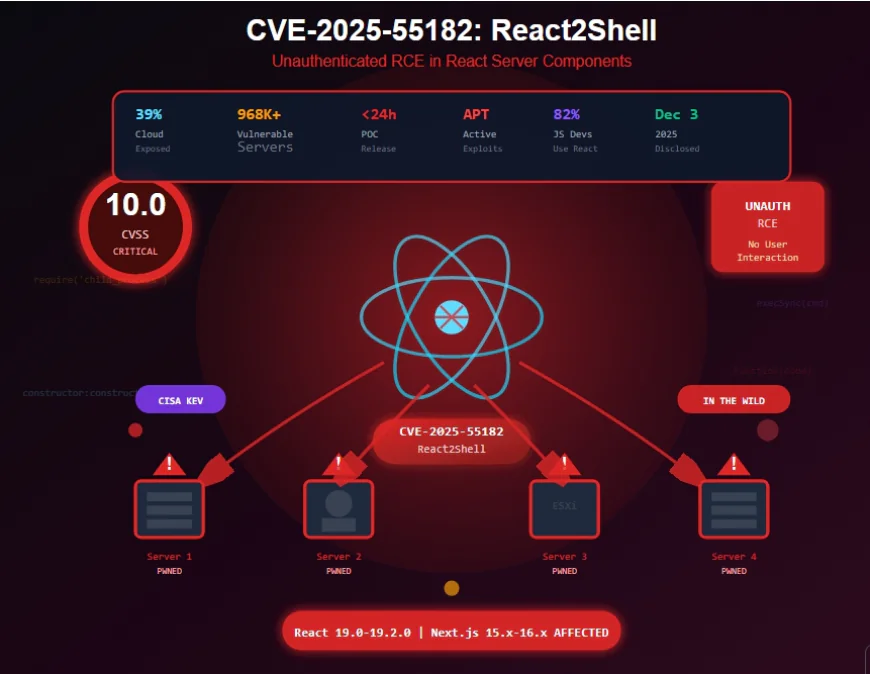
A critical vulnerability, tracked as CVE-2025-55182 and dubbed "React4Shell," has been discovered in React Server Components (RSC) and popular frameworks like Next.js. With a maximum CVSSv3 score of 10, this flaw allows unauthenticated attackers to execute arbitrary code on vulnerable servers, potentially leading to a complete system takeover. Immediate action is required to protect web assets.
CVE-2025-55182 (React4Shell) is a critical deserialization vulnerability affecting React Server Components and related frameworks.
Key Takeaways
- Critical Severity: CVE-2025-55182 has a CVSSv3 score of 10 (Critical), allowing unauthenticated remote code execution (RCE).
- Widespread Impact: Affects React Server Components (RSC) in React versions 19.x and many derivative frameworks including Next.js, React Router, and Waku. Approximately 39% of cloud infrastructures may be vulnerable.
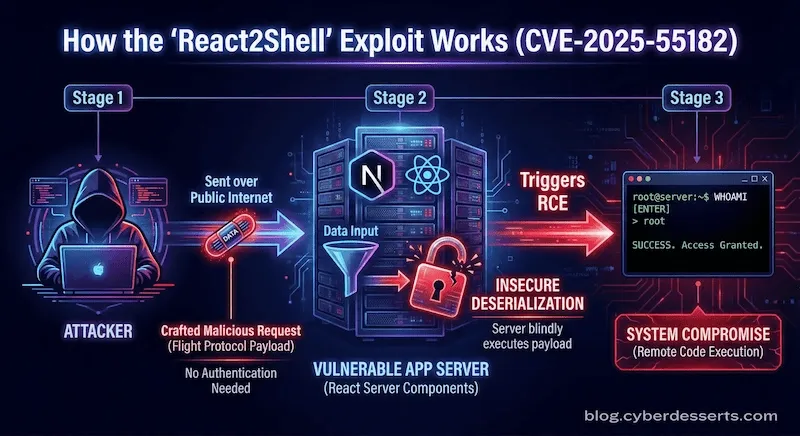
- Root Cause: The vulnerability lies in the unsafe deserialization of data streams in the React Flight protocol used for communication between client and server.
- Easy Exploitation: Attackers can send a specially crafted HTTP request to a vulnerable server before any authentication checks, triggering arbitrary code execution with the server's privileges.
- Immediate Mitigation: Update React to versions 19.0.1, 19.1.2, or 19.2.1. Update Next.js to versions 15.1.9, 15.2.6, 15.3.6, 15.4.8, 15.5.7, or 16.0.7.
- Defense in Depth: Major cloud providers (AWS, Cloudflare, Google Cloud, Vercel) have released WAF rules, but patching remains the only complete solution.
What is the React4Shell Vulnerability (CVE-2025-55182)?
Disclosed on December 3, 2025, this vulnerability affects React Server Components (RSC)—a feature introduced in React 18 that allows web pages to be assembled partly on the server for better performance. The flaw exists in the deserialization process of the Flight protocol, an HTTP-based protocol used for fast streaming of serialized data between client and server. Specifically, the unsafe handling of data streams in the react-server-dom-webpack, react-server-dom-turbopack, and react-server-dom-parcel packages allows attackers to inject and execute arbitrary code.
"To exploit the vulnerability, an attacker can send a simple HTTP request to the server, and even before authentication and any checks, this request can initiate the launch of a process on the server with React privileges."
— Kaspersky Blog, Dec 4, 2025
Affected Software & Versions
- React (RSC packages): Versions 19.0.0, 19.1.0, 19.1.1, 19.2.0
- Next.js: 15.0.4, 15.1.8, 15.2.5, 15.3.5, 15.4.7, 15.5.6, 16.0.6
- Other Frameworks: React Router RSC preview, Redwood SDK, Waku, RSC plugins for Vite and Parcel.
Patched Versions
- React: 19.0.1, 19.1.2, 19.2.1
- Next.js: 15.1.9, 15.2.6, 15.3.6, 15.4.8, 15.5.7, 16.0.7
- Update instructions for other frameworks available on the React blog.
🛡️ How to Protect Your Systems
🔧 1. Immediate Patching (Primary Mitigation)
Update all affected packages to the patched versions listed above. For Next.js projects, run npm install next@latest. For React projects, update the core packages and the specific server DOM packages. This is the only complete fix.
☁️ 2. Leverage Cloud Provider Protections
Major providers have released WAF rules that can block exploitation attempts:
- Cloudflare: Protects all customers (including free plan) if traffic is proxied through their WAF.
- AWS, Akamai, Google Cloud, Vercel: Have released rules that require manual activation or verification.
Important: WAF rules are only a temporary measure and do not replace patching.
🔒 3. Network-Level Controls
If you can't apply WAF rules, identify all servers with RSC endpoints and restrict access:
- Block requests from untrusted IP ranges for internal services.
- Strengthen IP reputation filtering and implement rate limiting for public services.
🕵️ 4. Monitoring & Incident Response
Use EPP/EDR agents on servers with RSC to detect post-exploitation anomalies. Investigate logs for suspicious requests. Signs of compromise include:
- Reconnaissance of the server environment.
- Access attempts to secrets (
.env, CI/CD tokens). - Installation of web shells.
If compromise is detected, rotate all secrets and keys immediately.
⚠️ Important Considerations
- Misconception: Not using RSC features does not guarantee safety. RSCs may be active by default in modern React/Next.js projects (e.g., those built with
create-next-app). - Exploit Availability: A proof-of-concept exploit is already available on GitHub, making mass exploitation highly likely.
- Scale: With major platforms like Airbnb and Netflix using React/Next.js, and 39% of cloud infrastructures running vulnerable components, the potential impact is massive.
💡 The Bottom Line
CVE-2025-55182 is a critical, easily exploitable vulnerability that requires immediate action. While WAF rules and network controls provide temporary mitigation, patching to the recommended versions is the only way to fully secure your applications. Given the public availability of exploit code and the widespread use of affected frameworks, treat this as an active threat and prioritize updates today.
Key Takeaways
- •This article highlights the latest trends in document technology
- •Practical insights for implementing PDF solutions in your workflow
- •Expert recommendations for document security and management
